![PDF] A Novel Approach for Security Testing of Client Server Based Applications using Misuse Deployment Diagrams, Misuse Cases and Threat Trees | Semantic Scholar PDF] A Novel Approach for Security Testing of Client Server Based Applications using Misuse Deployment Diagrams, Misuse Cases and Threat Trees | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/3a7ac83319973723a8447c3259ef226bbc9ab7bd/6-Table1-1.png)
PDF] A Novel Approach for Security Testing of Client Server Based Applications using Misuse Deployment Diagrams, Misuse Cases and Threat Trees | Semantic Scholar
Server application testing with Test Base for Microsoft 365 - Dr. Ware Technology Services - Microsoft Silver Partner

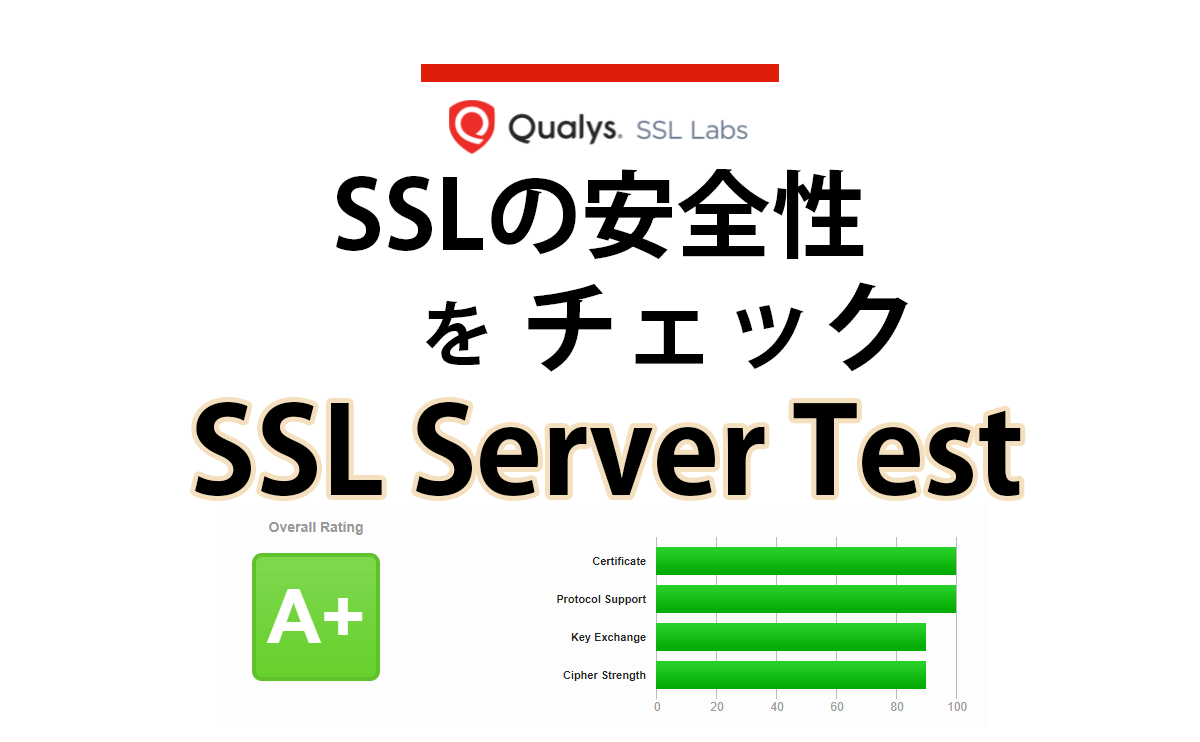
Infra Security (EMail Server)— How security gets compromised, How to take care of security, How to test & monitor your security provisioning | by Sujit Udhane | Medium