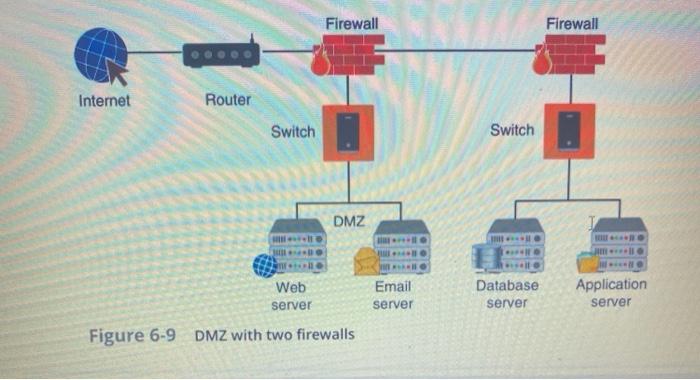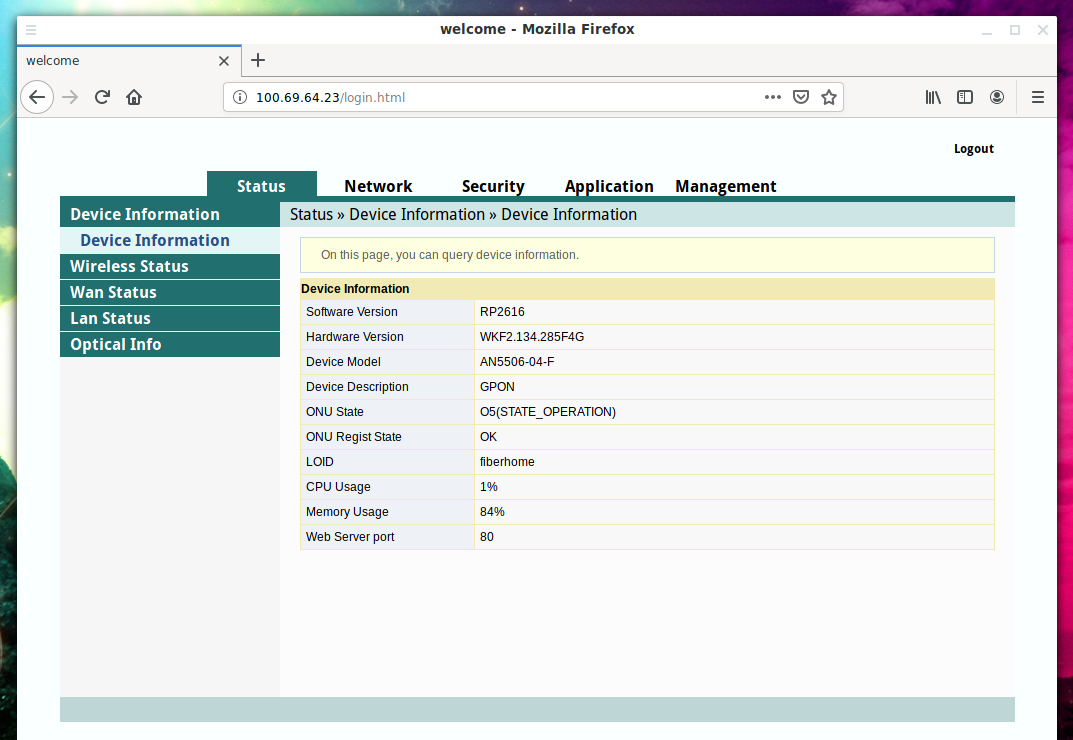
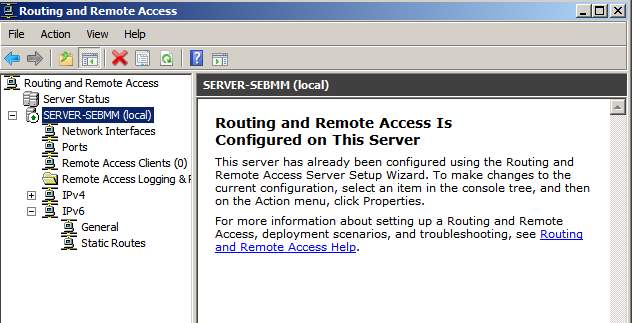
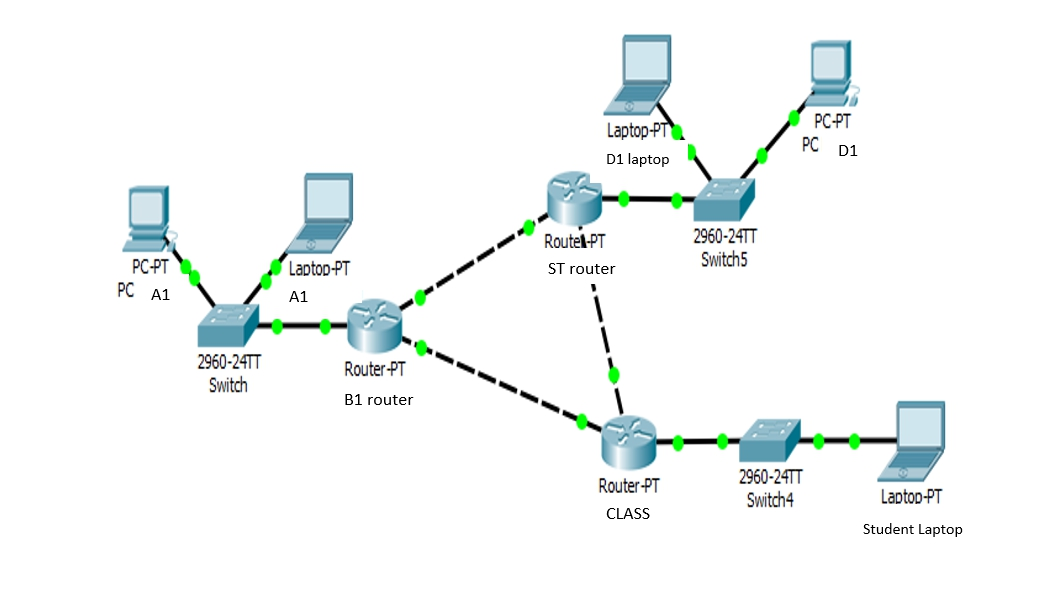
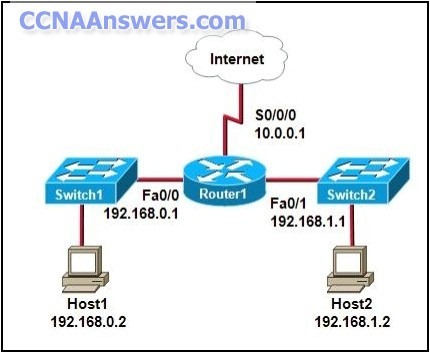
Attack on devices in the local network through a vulnerable router - Ethical hacking and penetration testing

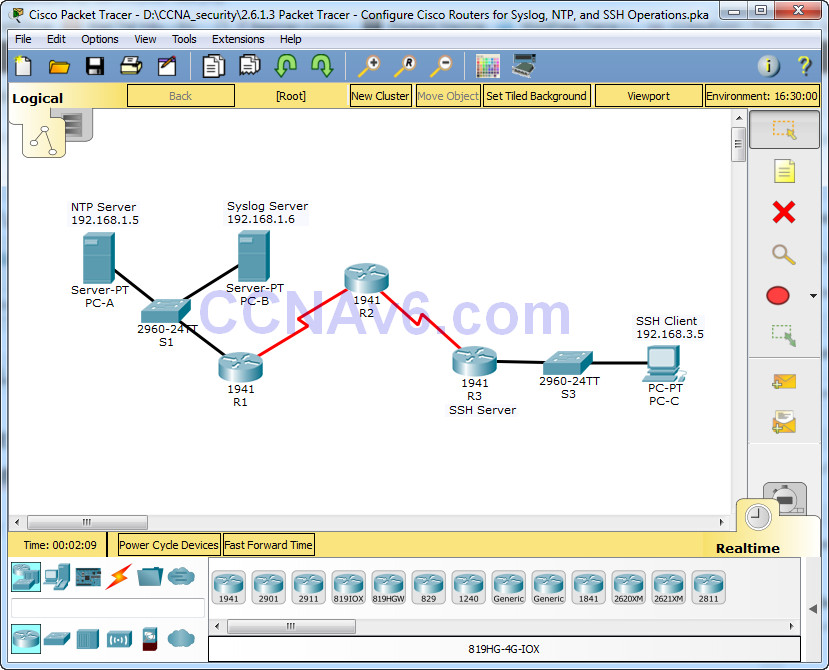
Internet Routing Architectures (2nd Edition) (Networking Technology) 2, Halabi, Sam, eBook - Amazon.com

Cisco Field Manual: Catalyst Switch Configuration: 0619472050439: Computer Science Books @ Amazon.com



![Cisco Field Manual: Catalyst Switch Configuration - [PDF Document] Cisco Field Manual: Catalyst Switch Configuration - [PDF Document]](https://cdn.vdocuments.mx/img/1200x630/reader024/reader/2021010422/57ade1f51a28abbe3a94b1b7/r-1.jpg?t=1639691567)